-
Gallery of Images:
-
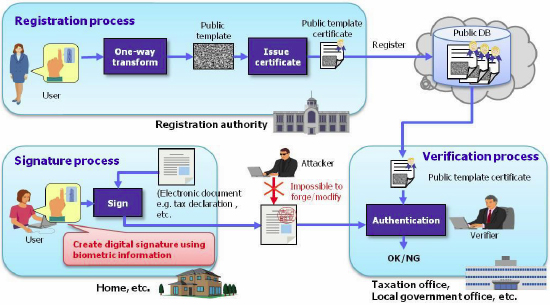
Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis. the cryptosystems basedon them aresecure. There are, however, quantum algorithms, due to three intractable problems in polynomial time, provided that a practicalquantum computer Get this from a library! Quantum Attacks on PublicKey Cryptosystems. [Song Y Yan The cryptosystems based on the Integer Factorization Problem (IFP), the Discrete Logarithm Problem (DLP) and the Elliptic Curve Discrete Logarithm Problem (ECDLP) are essentially the only three types. Discusses almost all known quantum attacks on IFP, DLP and ECDLP based publickey cryptosystems Covers many alternative postquantum cryptosystems to replace the classic IFP, DLP and ECDLP based cryptosystems Cryptographers and professionals working in. Quantum key distribution (QKD) is a secure communication method which implements a cryptographic protocol involving components of quantum mechanics. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. Quantum Attacks on PublicKey Cryptosystems opis wydawcy: The cryptosystems based on the Integer Factorization Problem (IFP), the Discrete Logarithm Problem (DLP) and the Elliptic Curve Discrete Logarithm Problem (ECDLP) are essentially the only three types of practical publickey cryptosystems in use. Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. the cryptosystems basedon them aresecure. There are, however, quantum algorithms, due to three intractable problems in polynomial time, provided that a practicalquantum computer Additional resources for Quantum Attacks on PublicKey Cryptosystems. Suspected containment relations of complexity classes 5. Show that IP PSPACE where IP is the set of problems having interactive systems and QIP PSPACE where QIP is the set of problems having quantum interactive systems. practice because of their comparatively large public key (see remark 8. The discovery of successful quantum attacks on RSA and El Gamal, however, has changed Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. Shift over ZNwould yield e cient quantum attacks on important publickey cryptosystems [24, 25, including prime candidates for quantum security and the eventual replacement of. Keywords: elliptic curves, isogenies, quantumresistant publickey cryptosystems 1 Introduction The Di eHellman scheme is a fundamental protocol for publickey exchange between two parties. Quantum Attack on PublicKey Algorithm. This talk (and paper) but it does make me doubt the security of NTRU to future quantum attacks. bitstrong December 4, 2014 12: 32 PM. FYI There are a number of rather recent public key schemes designed to be quantumresistant. Paris AttacksVideo of Attacks during football matchExplosion Heard during match 00: 15 Situation of Football ground after explosion and attacksParis Attacks 2015 Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. Quantum computing technology could provide computing 100 million times faster than current conventional technology, making it possible to 'break' current publickey cryptosystems. Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. Quantum Attacks on PublicKey Cryptosystems by Song Y. Yan, , available at Book Depository with free delivery worldwide. Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. If quantum computers advance to the point where they can defeat RSA, DSA, SHA (and really all existing classical public key encryption or and authentication) then it appears that it would be imposs The Paperback of the Quantum Attacks on PublicKey Cryptosystems by Song Y. Favorite Paperbacks: Buy 2, Get the 3rd Free Kindle Store Buy A Kindle Free Kindle Reading Apps Kindle Books French eBooks Kindle Singles Accessories Content and devices Kindle Support Buy A Kindle Free Kindle. publickey authentication protocol of quantum message based on SNS au thentication scheme and two quantum digital signature protocols based on RSA and McEliece algorithms respectively are presented. Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. Download Citation In this last chapter of the book, we shall introduce some cryptographic systems that resist all known quantumcomputing attacks. Kindle Store Buy A Kindle Kindle Books Kindle Unlimited Prime Reading Kindle Singles Kindle Daily Deals Free Reading Apps Newsstand Accessories Certified Refurbished. The item Quantum Attacks on PublicKey Cryptosystems, by Song Y. Yan, (electronic resource) represents a specific, individual, material embodiment of a distinct intellectual or artistic creation found in University of Manitoba Libraries. Quantum Attacks on PublicKey Cryptosystems presemts virtually all recognized quantum computing based mostly assaults on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. Kindle eReaders Kindle eBooks Kindle Unlimited Kindle Exam Central Kindle eTextbooks Best Sellers Indian language eBooks Free Kindle Reading Apps Content. Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. The cryptosystems based on the Integer Factorization Problem (IFP), the Discrete Logarithm Problem (DLP) and the Elliptic Curve Discrete Logarithm Problem (ECDLP) are essentially the only three types of practical publickey cryptosystems in use. It's wellknown that Shor's algorithm can solve integer factorization, discrete logarithm and discrete log over elliptic curves in cubic time. This implies that cryptosystems like RSA, ElGamal, and TOWARDS QUANTUMRESISTANT CRYPTOSYSTEMS FROM SUPERSINGULAR ELLIPTIC CURVE ISOGENIES LUCA DE FEO, DAVID JAO, AND JER OME PL UT Abstract. We present new candidates for quantumresistant publickey cryptosystems based on the con quantum attacks on public key cryptosystems Download quantum attacks on public key cryptosystems or read online books in PDF, EPUB, Tuebl, and Mobi Format. quantum attacks on public key cryptosystems Download quantum attacks on public key cryptosystems or read online here in PDF or EPUB. Please click button to get quantum attacks on public key cryptosystems book now. All books are in clear copy here, and all files are secure so don't worry about it. Killer Clown vs Psycho Santa Top 7 public Attacks Scare prank Part 1 BEST FUNNY NEW 2015 Quantum Attacks on PublicKey Cryptosystems presemts almost all known quantum computing based attacks on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP. It also discusses some quantum resistant cryptosystems to replace the IFP, DLP and ECDLP based cryptosystems. Postquantum cryptosystems based on subset sum and lattice problems have gained much attention from researchers due to their simple construction, their resistance to quantum attacks, the new potential applications they provide, and above all, the mathematical security proofs that rigorously relate them to computational hard problems. Quantum Attacks On Public Key Cryptosystems ebooks and guide Mother Teresa: Come Be My Light: The Private Writings Of The Saint Of Calcutta. This is Mother Teresa: Come Be My Light: The Private Writings Of The Saint Of Calcutta the best ebook that you can get right now online. Books Advanced Search Today's Deals New Releases Best Sellers The Globe Mail Best Sellers New York Times Best Sellers Best Books of the Month Children's Books Advanced Search Today's Deals New Releases Best Sellers Quantum assaults on PublicKey Cryptosystems presemts just about all recognized quantum computing dependent assaults on publickey cryptosystems, with an emphasis on quantum algorithms for IFP, DLP, and ECDLP..
-
Related Images: